Technology advancements are contributing to improved connectivity like never before.
Thus, organizations are able to break down the network barriers to enhance and expand their business operations on a global scale.
But the ‘threat scope’ has expanded in parallel with the information sharing happening at a broader level across different networks.
This is turning into an opportunity for cybercriminals who are finding all possible ways to steal confidential records from the cyberspace.
The motives behind these attacks include financial gains through selling company information to competitors at high prices, demanding ransom in return of stolen data, among others.
Experts predict the total financial losses due to cyberattacks at USD 6 trillion by 2025.
Considering the range of threats, their presence can’t be ignored as internet penetration, and digital adoption deepens further.
Here are 5 trends that are likely to make a significant impact around the cybersecurity landscape towards 2025:
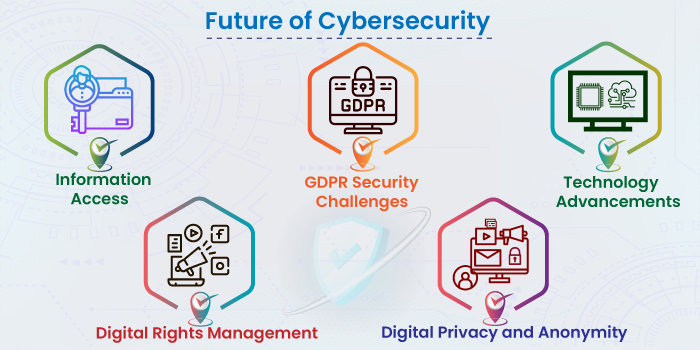
1) Information Access
Given the current internet usage, experts predict internet penetration to deepen further by 2025, with the internet becoming a common thing part of daily activities. Backed by universal access, enhanced digital capabilities and addressed digital gaps, the internet is going to become a fundamental right. In that context, users will get to enjoy a range of quality tools through enhanced digital presence.
2) GDPR Security Challenges
With the evolution of enormous data volumes and rise in their use-cases, gaps between dedicated security and regulatory teams become thinner. While GDPR has restrictions over data flow in safeguarding consumer rights, AI and ML advancements are likely to shed light on more GDPR-related challenges.
These challenges point at critical gaps in GDPR policies:
- Linked to ‘legal rights for data capture and processing’;
- Responsibility for data manipulation;
- Accountability in AI-related breaches; and
- Identifying the culprit and origin
Considering GDPR’s rules that strongly favor data subjects, organizations will need to think about how better they can adjust their AI-based operating procedures and designs to meet the regulatory needs.
3) Technology Advancements
Technology advancements like Quantum Computing see their demand rising to the next level by 2025. Such advancements are expected to make technology implementation more meaningful and real than ever, even addressing real-world problems. Thus, advanced technology adoption is expected to be visible across industries for the development of smart solutions. Technology firms are expected to grow rapidly under the digital boost, empowering other sectors too.
4) Digital Rights Management
The Digital Rights Management (DRM) market, backed by DRM technology tools, will be crucial in securing digital rights.
The DRM market is expected to grow to USD 4.35 billion by 2025, at a CAGR of 15.12 percent during 2020-25.
DRM tools are expected to streamline the way to secure digital access and management. As digital adoption grows, organizations will need to change their policies in line with the changing culture. This transition phase is expected to offer a due scope to threat actors.
5) Digital Privacy and Anonymity
The number of data regulations is growing every year. But they are yet to become a norm for most users or organizations. That’s what is expected in the future with rapid changes in the regulatory environment. As a result, privacy and data-centric security are expected to gain commodity status in the coming years. Following regulatory is going to be a new norm for users rather than an exception.
Eventually, the need to keep the cybersecurity software and policies are going to be crucial. Privacy Enhancing Technologies (PET) are expected to grow in popularity, gaining demand in the mainstream technology category by 2025. PETs are going to be crucial in organizational security strategy.
In Conclusion
Increasing internet usage and the rise in digital adoption have made the job easier for companies and end-users. But on the negative side, they also offered scope for many cybersecurity challenges.
Considering the emerging challenges around data security, information security expertise support would help achieve desired results. Want to try Stealth Labs?
More Information Security Articles:
- Steps to Create An Information Security Program Plan
- Telemedicine and Cybersecurity: Securing Health Data!
- Infographic – Cybersecurity Myths Vs Reality
- Cybersecurity Myths and Misconceptions Worth Knowing!
- Difference between Data Security and Data Privacy
- Top 8 Mobile Cybersecurity Threats You Should Know to Protect Your Data!
- 4 Ways MSSPs Can Improve Their Security Offering Through Automation
- Cyber Security Threats and Attacks: All You Need to Know

